Hi folks,
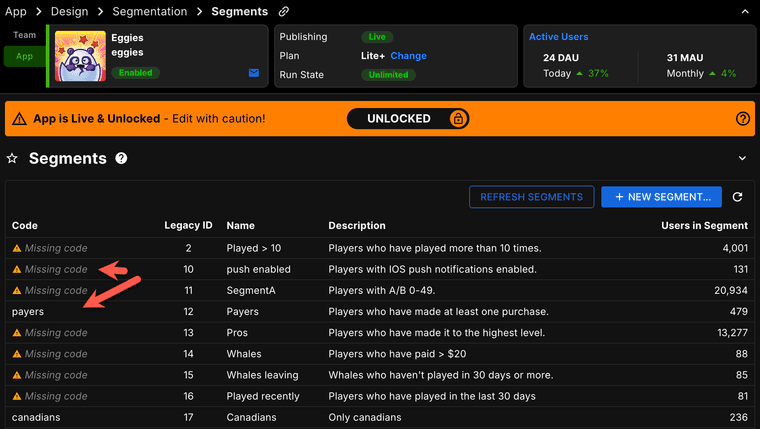
A quick reminder that we are moving from Segment IDs (system-assigned numbers) to SegmentCodes (which you get to pick!).
Unless... you DON'T pick them in time, and we have to auto-generate them for you!
[And note - codes can't be changed once set - so you probably want to do it yourself.]
More info here - https://updates.braincloudservers.com/action-set-your-segment-codes-9U2BO
Paul.
[PS - there was a Portal bug that was preventing the code from being editable for some users. That has now been fixed!]